PassLeader just published the NEWEST Fortinet NSE5 exam dumps! And, PassLeader offer two types of the NSE5 dumps — NSE5 VCE dumps and NSE5 PDF dumps, both VCE and PDF contain the NEWEST NSE5 exam questions, they will help you PASSING the Fortinet NSE5 exam easily! Now, get the NEWEST NSE5 dumps in VCE and PDF from PassLeader — http://www.passleader.com/nse5.html (320 Q&As Dumps)
What’s more, part of that PassLeader NSE5 dumps now are free — https://drive.google.com/open?id=0B-ob6L_QjGLpU0FrbTh1X3JMSmM
QUESTION 201
Which of the following describes the difference between the ban and quarantine actions?
A. A ban action prevents future transactions using the same protocol which triggered the ban. A qarantine action blocks all future transactions, regardless of the protocol.
B. A ban action blocks the transaction. A quarantine action archives the data.
C. A ban action has a finite duration. A quarantine action must be removed by an administrator.
D. A ban action is used for known users. A quarantine action is used for unknown users.
Answer: A
QUESTION 202
Which of the following describes the best custom signature for detecting the use of the word “Fortinet” in chat applications?
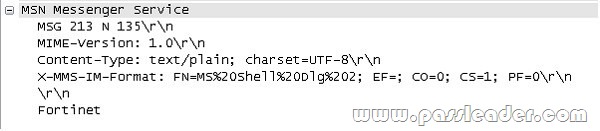
A. The sample packet trace illustrated in the exhibit provides details on the packet that requires detection.
F-SBID( –protocol tcp; –flow from_client; –pattern “X-MMS-IM-Format”; –pattern “fortinet”; –no_case; )
B. F-SBID( –protocol tcp; –flow from_client; –pattern “fortinet”; –no_case; )
C. F-SBID( –protocol tcp; –flow from_client; –pattern “X-MMS-IM-Format”; –pattern “fortinet”; –within 20; –no_case; )
D. F-SBID( –protocol tcp; –flow from_client; –pattern “X-MMS-IM-Format”; –pattern “fortinet”; –within 20; )
Answer: A
QUESTION 203
Which of the following cannot be used in conjunction with the endpoint compliance check?
A. HTTP Challenge Redirect to a Secure Channel (HTTPS) in the Authentication Settings.
B. Any form of firewall policy authentication.
C. WAN optimization.
D. Traffic shaping.
Answer: A
QUESTION 204
In order to load-share traffic using multiple static routes, the routes must be configured with ____.
A. the same distance and same priority.
B. the same distance and the same weight.
C. the same distance but each of them must be assigned a unique priority.
D. a distance equal to its desired weight for ECMP but all must have the same priority.
Answer: A
QUESTION 205
When configuring a server load balanced virtual IP, which of the following is the best distribution algorithm to be used in applications where the same physical destination server must be maintained between sessions?
A. Static
B. Round robin
C. Weighted round robin
D. Least connected
Answer: A
QUESTION 206
If Routing Information Protocol (RIP) version 1 or version 2 has already been configured on a FortiGate unit, which of the following statements is correct if the routes learned through RIP need to be advertised into Open Shortest Path First (OSPF)?
A. The FortiGate unit will automatically announce all routes learned through RIP v1 or v2 to its OSPF neighbors.
B. The FortiGate unit will automatically announce all routes learned only through RIP v2 to its OSPF neighbors.
C. At a minimum, the network administrator needs to enable Redistribute RIP in the OSPF Advanced Options.
D. The network administrator needs to configure a RIP to OSPF announce policy as part of the RIP settings.
E. At a minimum, the network administrator needs to enable Redistribute Default in the OSPF Advanced Options.
Answer: C
QUESTION 207
Which of the following statements are correct regarding the configuration of a FortiGate unit as an SSL VPN gateway? (Select all that apply.)
A. Tunnel mode can only be used if the SSL VPN user groups have at least one Host Check option enabled.
B. The specific routes needed to access internal resources through an SSL VPN connection in tunnel mode from the client computer are defined in the routing widget associated with the SSL VPN portal.
C. In order to apply a portal to a user, that user must belong to an SSL VPN user group.
D. The portal settings specify whether the connection will operate in web-only or tunnel mode.
Answer: CD
QUESTION 208
An administrator is examining the attack logs and notices the following entry:
device_id=FG100A3907508962 log_id=18432 subtype=anomaly type=ips timestamp=1270017358 pri=alert itime=1270017893 severity=critical src=192.168.1.52 dst=64.64.64.64 src_int=internal serial=0 status=clear_session proto=6 service=http vd=root count=1 src_port=35094 dst_port=80 attack_id=100663402 sensor=protect- servers ref=http://www.fortinet.com/ids/VID100663402 msg=”anomaly: tcp_src_session, 2 > threshold 1″ policyid=0 carrier_ep=N/A profile=N/A dst_int=N/A user=N/A group=N/A
Based solely upon this log message, which of the following statements is correct?
A. This attack was blocked by the HTTP protocol decoder.
B. This attack was caught by the DoS sensor “protect-servers”.
C. This attack was launched against the FortiGate unit itself rather than a host behind the FortiGate unit.
D. The number of concurrent connections to destination IP address 64.64.64.64 has exceeded the configured threshold.
Answer: B
QUESTION 209
Which of the following pieces of information can be included in the Destination Address field of a firewall policy? (Select all that apply.)
A. An IP address pool.
B. A virtual IP address.
C. An actual IP address or an IP address group.
D. An FQDN or Geographic value(s).
Answer: BCD
QUESTION 210
You wish to create a firewall policy that applies only to traffic intended for your web server. The server has an IP address of 192.168.2.2 and belongs to a class C subnet. When defining the firewall address for use in this policy, which one of the following addressing formats is correct?
A. 192.168.2.0 / 255.255.255.0
B. 192.168.2.2 / 255.255.255.0
C. 192.168.2.0 / 255.255.255.255
D. 192.168.2.2 / 255.255.255.255
Answer: D
QUESTION 211
Examine the exhibit shown below; then answer the question following it.
Which of the following statements best describes the green status indicators that appear next to the different FortiGuard Distribution Network services as illustrated in the exhibit?
A. They indicate that the FortiGate unit is able to connect to the FortiGuard Distribution Network.
B. They indicate that the FortiGate unit has the latest updates that are available from the FortiGuard Distribution Network.
C. They indicate that updates are available and should be downloaded from the FortiGuard Distribution Network to the FortiGate unit.
D. They indicate that the FortiGate unit is in the process of downloading updates from the FortiGuard Distribution Network.
Answer: A
QUESTION 212
Each UTM feature has configurable UTM objects such as sensors, profiles or lists that define how the feature will function. How are UTM features applied to traffic?
A. One or more UTM features are enabled in a firewall policy.
B. In the system configuration for that UTM feature, you can identify the policies to which the feature is to be applied.
C. Enable the appropriate UTM objects and identify one of them as the default.
D. For each UTM object, identify which policy will use it.
Answer: A
QUESTION 213
The command structure of the FortiGate CLI consists of commands, objects, branches, tables, and parameters. Which of the following items describes user?
A. A command.
B. An object.
C. A table.
D. A parameter.
Answer: B
QUESTION 214
Which of the following is an advantage of using SNMP v3 instead of SNMP v1/v2 when querying the FortiGate unit?
A. Packet encryption
B. MIB-based report uploads
C. SNMP access limits through access lists
D. Running SNMP service on a non-standard port is possible
Answer: A
QUESTION 215
Which of the following methods can be used to access the CLI? (Select all that apply.)
A. By using a direct connection to a serial console.
B. By using the CLI console window in the GUI.
C. By using an SSH connection.
D. By using a Telnet connection.
Answer: ABCD
QUESTION 216
Which of the following regular expression patterns will make the terms “confidential data” case insensitive?
A. \[confidential data]
B. /confidential data/i
C. i/confidential data/
D. “confidential data”
E. /confidential data/c
Answer: B
QUESTION 217
Examine the firewall configuration shown below; then answer the question following it.
Which of the following statements are correct based on the firewall configuration illustrated in the exhibit? (Select all that apply.)
A. A user can access the Internet using only the protocols that are supported by user authentication.
B. A user can access the Internet using any protocol except HTTP, HTTPS, Telnet, and FTP. These require authentication before the user will be allowed access.
C. A user must authenticate using the HTTP, HTTPS, SSH, FTP, or Telnet protocol before they can access any services.
D. A user cannot access the Internet using any protocols unless the user has passed firewall authentication.
Answer: AD
QUESTION 218
When backing up the configuration file on a FortiGate unit, the contents can be encrypted by enabling the encrypt option and supplying a password. If the password is forgotten, the configuration file can still be restored using which of the following methods?
A. Selecting the recover password option during the restore process.
B. Having the password emailed to the administrative user by selecting the Forgot Password option.
C. Sending the configuration file to Fortinet Support for decryption.
D. If the password is forgotten, there is no way to use the file.
Answer: D
QUESTION 219
Which of the following statements is correct about how the FortiGate unit verifies username and password during user authentication?
A. If a remote server is included in a user group, it will be checked before local accounts.
B. An administrator can define a local account for which the password must be verified by querying a remote server.
C. If authentication fails with a local password, the FortiGate unit will query the authentication server if the local user is configured with both a local password and an authentication server.
D. The FortiGate unit will only attempt to authenticate against Active Directory if Fortinet Server Authentication Extensions are installed and configured.
Answer: B
QUESTION 220
A FortiGate unit is configured with three Virtual Domains (VDOMs) as illustrated in the exhibit.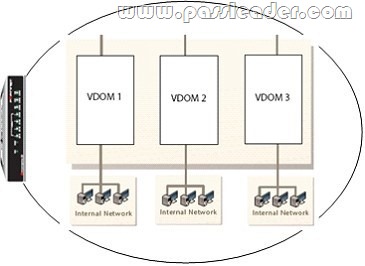
Which of the following statements are correct regarding these VDOMs? (Select all that apply.)
A. The FortiGate unit supports any combination of these VDOMs in NAT/Route and Transparent modes.
B. The FortiGate unit must be a model 1000 or above to support multiple VDOMs.
C. A license had to be purchased and applied to the FortiGate unit before VDOM mode could be enabled.
D. All VDOMs must operate in the same mode.
E. Changing a VDOM operational mode requires a reboot of the FortiGate unit.
F. An admin account can be assigned to one VDOM or it can have access to all three VDOMs.
Answer: AF
QUESTION 221
The diag sys session list command is executed in the CLI. The output of this command is shown in the exhibit.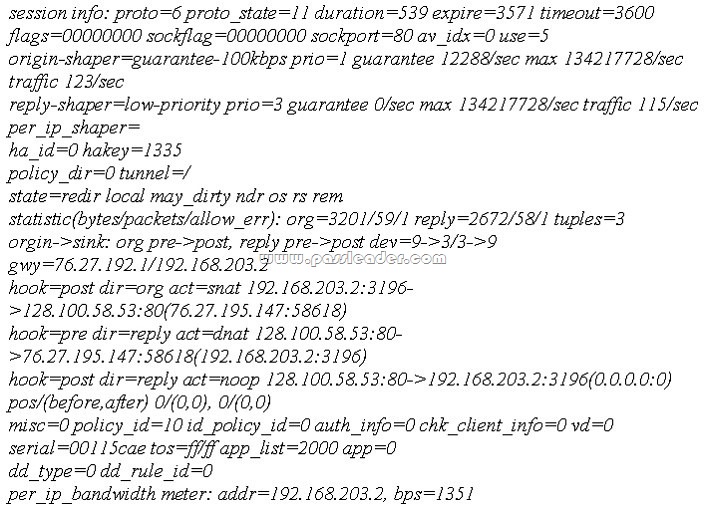
Based on the output from this command, which of the following statements is correct?
A. This is a UDP session.
B. Traffic shaping is being applied to this session.
C. This is an ICMP session.
D. This traffic has been authenticated.
E. This session matches a firewall policy with ID 5.
Answer: B
QUESTION 222
Which of the following must be configured on a FortiGate unit to redirect content requests to remote web cache servers?
A. WCCP must be enabled on the interface facing the Web cache.
B. You must enabled explicit Web-proxy on the incoming interface.
C. WCCP must be enabled as a global setting on the FortiGate unit.
D. WCCP must be enabled on all interfaces on the FortiGate unit through which HTTP traffic is passing.
Answer: A
QUESTION 223
What advantages are there in using a fully Meshed IPSec VPN configuration instead of a hub and spoke set of IPSec tunnels?
A. Using a hub and spoke topology is required to achieve full redundancy.
B. Using a full mesh topology simplifies configuration.
C. Using a full mesh topology provides stronger encryption.
D. Full mesh topology is the most fault-tolerant configuration.
Answer: D
QUESTION 224
The transfer of encrypted files or the use of encrypted protocols between users and servers on the internet can frustrate the efforts of administrators attempting to monitor traffic passing through the FortiGate unit and ensuring user compliance to corporate rules. Which of the following items will allow the administrator to control the transfer of encrypted data through the FortiGate unit? (Select all that apply.)
A. Encrypted protocols can be scanned through the use of the SSL proxy.
B. DLP rules can be used to block the transmission of encrypted files.
C. Firewall authentication can be enabled in the firewall policy, preventing the use of encrypted communications channels.
D. Application control can be used to monitor the use of encrypted protocols; alerts can be sent to the administrator through email when the use of encrypted protocols is attempted.
Answer: ABD
QUESTION 225
The following diagnostic output is displayed in the CLI:
diag firewall auth list
policy iD. 9, srC. 192.168.3.168, action: accept, timeout: 13427
user: forticlient_chk_only, group:
flag (80020): auth timeout_ext, flag2 (40): exact
group iD. 0, av group: 0
—– 1 listed, 0 filtered —–
Based on this output, which of the following statements is correct?
A. Firewall policy 9 has endpoint compliance enabled but not firewall authentication.
B. The client check that is part of an SSL VPN connection attempt failed.
C. This user has been associated with a guest profile as evidenced by the group id of 0.
D. An auth-keepalive value has been enabled.
Answer: A
Learning the PassLeader NSE5 dumps with VCE and PDF for 100% passing Fortinet certification — http://www.passleader.com/nse5.html (320 Q&As Dumps)
BONUS!!! Download part of PassLeader NSE5 dumps for free — https://drive.google.com/open?id=0B-ob6L_QjGLpU0FrbTh1X3JMSmM